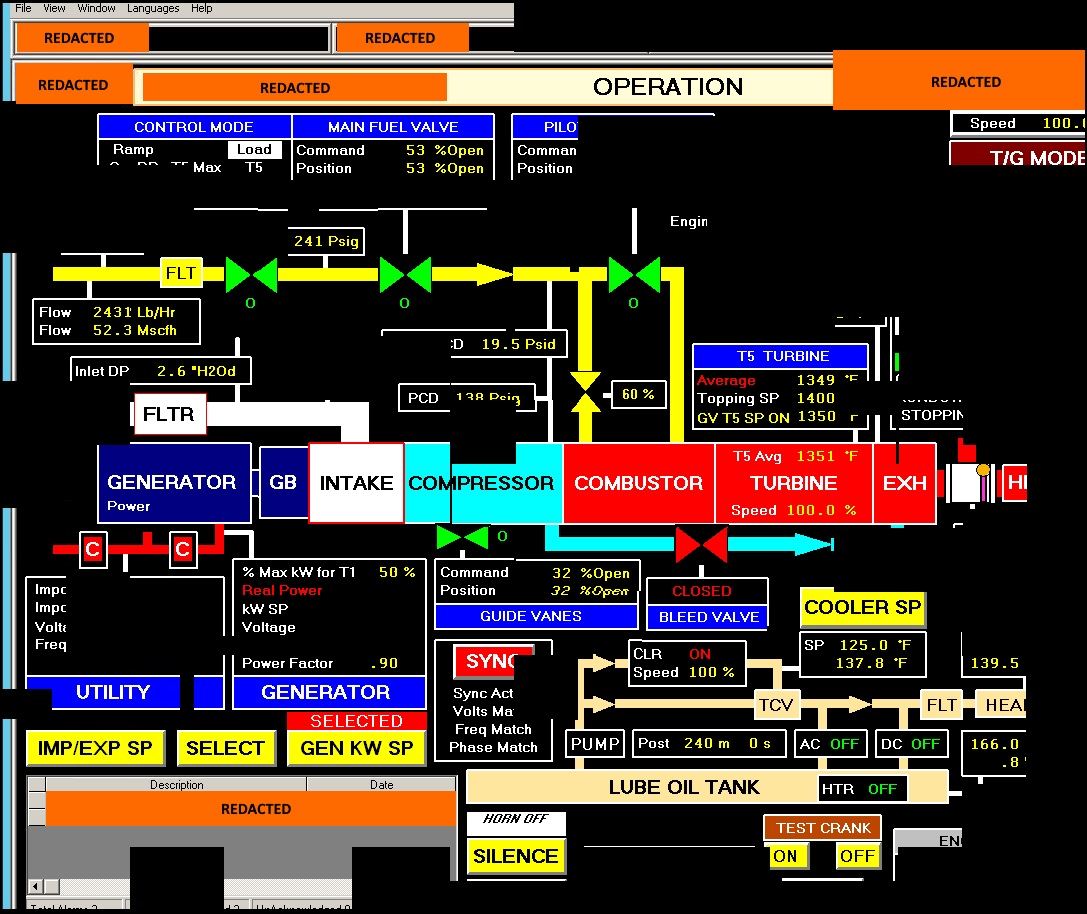
In multiple instances, the threat actors accessed workstations and servers on a corporate network that contained data output from control systems within energy generation facilities. Credit: Courtesy of U.S. Department of Homeland Security
A successful hack of critical U.S. industries by Russian agents was largely preventable, a cybersecurity expert at Ohio State said.
A Russian-sponsored hacking campaign aimed at U.S. business fields including manufacturers and energy producers was revealed in a joint statement by the FBI and Department of Homeland Security on March 15. Hackers successfully penetrated many targets since starting the attacks in 2016 and gained access that could have been used to remotely control critical operations.
Steven Romig, the director of security operations in Ohio State’s Office of the Chief Information Officer, said the attacks could have been avoided with education and simple security measures.
Passwords to a variety of systems were stolen during the Russian hacking, according to the FBI report, but only environments without multifactor authentication — an additional step to verify a user’s identity before gaining access to a secured system — were infiltrated.
“It’s kind of hard for me to believe, in this day and age, having any part of our critical infrastructure that doesn’t require multifactor authentication,” Romig said.
An example of multifactor authentication students and staff at Ohio State use is Duo Mobile, the service that provides push notification sent to phone when logging into BuckeyeLink. Romig said the inconvenience is worth the added security.
“People tend to complain a lot about the security things that security practitioners advise them to do,” he said, “But we advise them for a reason.”
To initially gain the credentials, hackers used a process called spear phishing, according to the report. The method is a specifically targeted and more advanced version of a standard phishing attack, Romig said.
“[Spear phishing is] targeted at people who would give [hackers] strategic access to things. So, they might target the executive of a company … or target people that have technical oversight to facilities,” he said.
Romig said the attacks are less frequent than regular phishing, though common enough that most users have experienced the method.
“[Students] have probably seen any number of phishing attacks that target people at the university to try to get access to [Ohio State’s] systems,” he said.
Romig’s office regularly engages in campaigns to educate the Ohio State community about phishing techniques. Those targeted by the Russian hack would benefit from similar training, Romig said.
According to the report, agents attached Microsoft Word documents to some emails containing hyperlinks that went to an external file-sharing site requesting authentication. The site was automatically sent a hash, a coded version of the user’s password designed to verify credentials without revealing them. Hackers were able to recover passwords using the hash.
Romig said he had not heard of the method being used before.
“It’s clever,” he said. “But once you know the trick and how to implement the trick, it’s a piece of cake.”
Once access is gained, Romig said what hackers do next depends on their goals — which could be stealing information or gaining control over the system.
“They could have many different purposes in mind,” he said.
Higher education was not among the impacted industries listed in the report, though Romig said his office still received information from sources including the Department of Homeland Security and the FBI detailing how to identify signs the university was targeted in these attacks.
“Now that we have that information we can go out and search our systems for them and see what we can see,” he said.
Ohio State has been targeted in attacks hosted by nation-states before, Romig said, but how often is unknown because tracing an attack to its host is difficult.
“The Chinese are often accused of being behind attacks against universities to try to get access to intellectual property. We see all kinds of attacks every day at the university,” he said. “How many of those are because the Chinese are trying to get into our systems? We’ve got no idea for the most part.”


